Why SaaS Companies Need Penetration Testing
SaaS platforms are high-value targets. Your application is internet-facing by design, handles sensitive customer data, and operates in a multi-tenant environment where a single vulnerability can expose every customer on your platform. Attackers know this, and so do your customers, investors, and compliance auditors.
Unlike traditional on-premises software, SaaS applications have a continuously evolving attack surface. Every feature release, API endpoint, and infrastructure change introduces potential security gaps. Automated vulnerability scanners catch known issues, but they cannot identify the business logic flaws, authentication bypasses, and tenant isolation failures that represent the most critical risks to a SaaS platform.
Penetration testing gives SaaS companies a realistic assessment of how an attacker would target their platform. It validates that your security controls actually work under adversarial conditions, not just in theory.
The SaaS-Specific Threat Landscape
SaaS applications face a distinct set of security challenges that generic penetration testing approaches often miss. Understanding these threats is the first step toward building an effective testing program.
Multi-Tenancy and Tenant Isolation
Multi-tenant architectures are the backbone of most SaaS platforms, but they also introduce one of the most dangerous vulnerability classes: tenant isolation failures. If an attacker on one tenant account can access data belonging to another tenant, the impact is catastrophic. This includes:
- Insecure Direct Object References (IDOR) — manipulating resource identifiers to access another tenant’s data
- Shared infrastructure leakage — database connection pooling, caching layers, or file storage that bleeds across tenants
- Privilege escalation across tenant boundaries — exploiting role-based access control flaws to gain cross-tenant access
- API parameter tampering — modifying tenant identifiers in API requests to bypass authorization checks
Automated scanners cannot reliably detect these issues because they require contextual understanding of how your application separates tenant data.
API Security
Modern SaaS platforms are API-first. Your REST and GraphQL endpoints are your application’s real attack surface, and they often expose more functionality than the web interface itself. Common API security issues in SaaS platforms include:
- Broken authentication and session management
- Missing or inconsistent authorization checks across endpoints
- Mass assignment vulnerabilities allowing attackers to modify restricted fields
- Rate limiting gaps that enable brute force and enumeration attacks
- Excessive data exposure in API responses
Authentication and Identity
SaaS platforms typically support multiple authentication methods including SSO, OAuth, SAML, and magic links. Each integration point is a potential weakness. Penetration testing should validate that authentication flows cannot be bypassed, session tokens are properly managed, and account takeover paths are closed.
CI/CD and Supply Chain Risks
Your deployment pipeline is part of your attack surface. Compromised dependencies, insecure build configurations, and exposed secrets in repositories can give attackers access to your production environment without ever touching your application directly.
What Should a SaaS Penetration Test Cover?
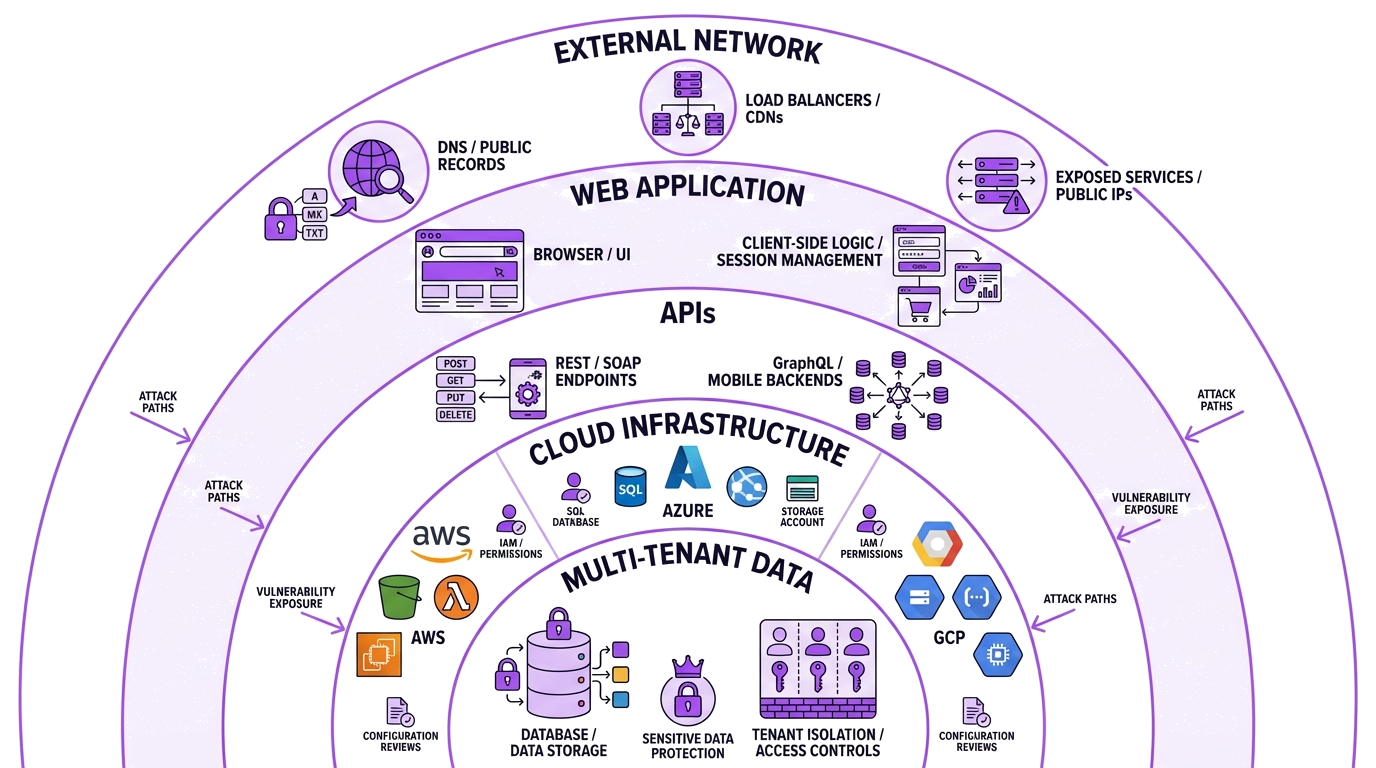
A comprehensive penetration test for a SaaS company should go beyond a standard web application penetration test and address the platform holistically. Here is what a thorough engagement should include.
Web Application Testing
The core of any SaaS penetration test. This covers the customer-facing application, admin panels, and any internal tooling exposed through the web. Testing should address the OWASP Top 10 as a baseline, then go deeper into application-specific logic, workflow manipulation, and access control enforcement.
API Testing
Every API endpoint your platform exposes, whether documented or not, should be tested. This includes public APIs, internal microservice communication, webhooks, and third-party integrations. Testers should examine authentication, authorization, input validation, and data exposure across the full API surface.
Cloud Infrastructure
Most SaaS platforms run on AWS, Azure, or GCP. Cloud penetration testing evaluates your cloud configuration, IAM policies, storage bucket permissions, network segmentation, and serverless function security. Misconfigured cloud resources are one of the most common causes of SaaS data breaches.
External Network Testing
Your external network attack surface includes everything reachable from the internet: load balancers, DNS configuration, email security, exposed management interfaces, and any services running on public IP addresses. Even well-architected SaaS platforms sometimes leave development or staging environments exposed.
Multi-Tenant Isolation Testing
This is the SaaS-specific testing that matters most. Testers should attempt to break tenant boundaries at every layer: application, database, file storage, caching, and messaging. This requires manual testing with multiple tenant accounts and a deep understanding of your application’s architecture.
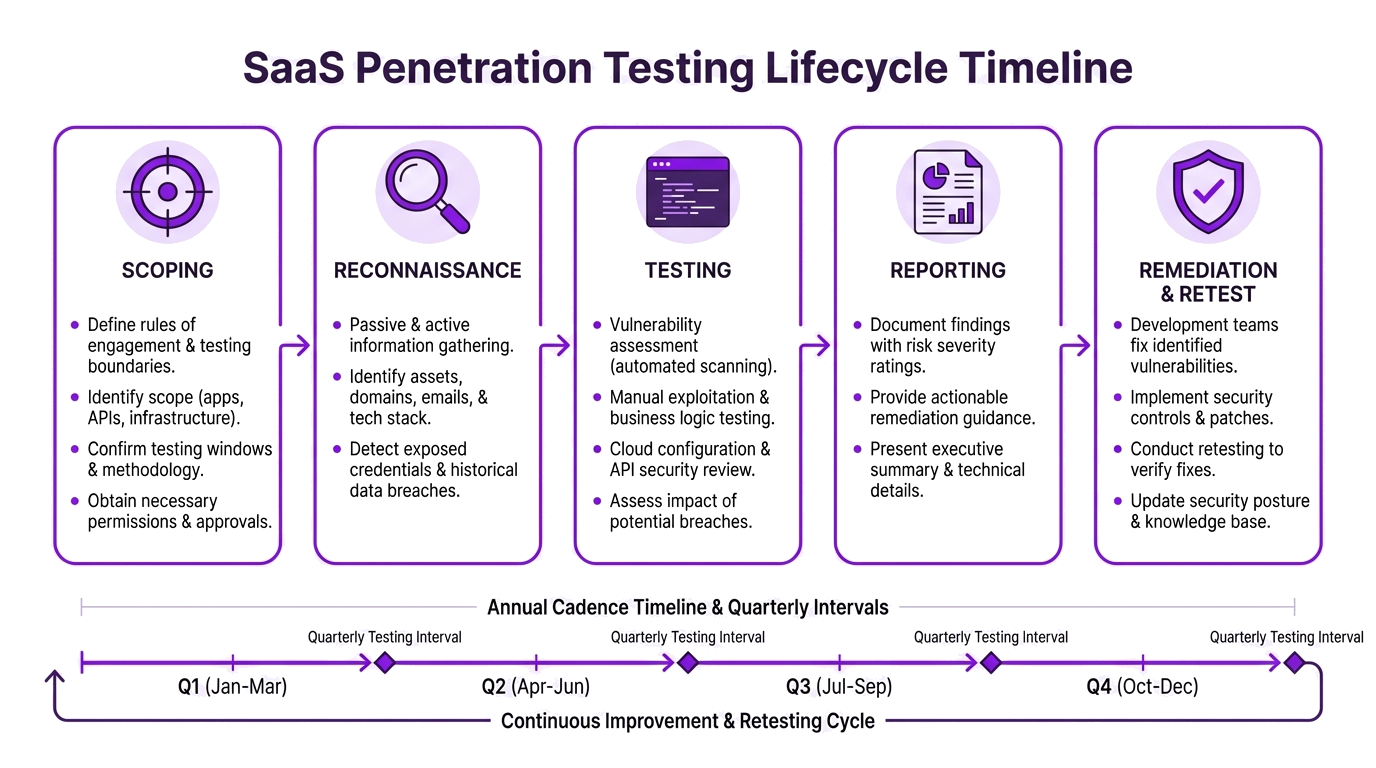
When Should SaaS Companies Get Penetration Tested?
Before Major Milestones
Penetration testing is often required, or at minimum expected, at key business milestones:
- Before launching a new product or major feature — validate security before customers are exposed
- Before closing enterprise deals — large customers will ask for recent penetration test reports as part of vendor security reviews
- Before a funding round — investors increasingly evaluate security posture during due diligence
- After a significant architectural change — migrating databases, changing authentication providers, or re-architecting APIs all warrant retesting
For Compliance Requirements
SaaS companies serving regulated industries will encounter penetration testing requirements from multiple frameworks:
| Compliance Framework | Penetration Testing Requirement |
|---|---|
| SOC 2 | Penetration testing supports Trust Services Criteria, particularly CC7.1 and CC7.2 |
| PCI DSS 4.0 | Required annually and after significant changes for organizations handling payment data |
| ISO 27001 | Required as part of Annex A technical vulnerability management controls |
| PIPEDA | Recommended as part of demonstrating reasonable security safeguards |
| HIPAA | Expected as part of the technical security assessment requirement |
| Cyber Insurance | Increasingly required by underwriters as a condition of coverage |
For compliance-specific engagements, DarkPoint offers dedicated PCI DSS penetration testing and SOC 2 penetration testing services designed to meet the specific requirements of each framework.
On a Regular Cadence
At minimum, SaaS companies should conduct a full penetration test annually. Companies with rapid release cycles, high-value data, or compliance obligations should test more frequently, either quarterly or after every major release. Between full engagements, consider supplementing with targeted assessments of new features or API endpoints.
How to Choose a Penetration Testing Provider for Your SaaS Platform
Not every penetration testing firm is equipped to test SaaS applications effectively. Here is what to look for when evaluating providers.
SaaS and Cloud Experience
Your provider should have demonstrated experience testing multi-tenant SaaS platforms, not just traditional web applications. Ask about their experience with your specific cloud provider (AWS, Azure, GCP) and whether they understand container orchestration, serverless architectures, and microservice communication patterns.
Manual-First Methodology
Automated scanning tools miss the vulnerabilities that matter most to SaaS companies: business logic flaws, tenant isolation failures, and chained attack paths. Your provider should be able to articulate exactly how they perform manual testing beyond running automated tools. Ask what percentage of the engagement involves manual testing — anything below 70% should raise concerns.
Relevant Certifications
Look for consultants holding hands-on offensive security certifications such as OSCP, OSWE, and OSCE. These certifications require practical examination and demonstrate real-world testing ability. Be cautious of firms that only list theoretical certifications like CEH without practical credentials to back them up.
Actionable Reporting
The penetration test report is the primary deliverable your development team will work from. It should include:
- Clear vulnerability descriptions with business impact context
- Step-by-step reproduction instructions your developers can follow
- Proof-of-concept evidence for every finding
- Prioritized remediation guidance
- An executive summary suitable for sharing with stakeholders and customers
Ask to see a sample report before signing. If the report looks like automated scanner output, the testing likely is too.
Remediation Retesting
After your team fixes the identified vulnerabilities, the provider should retest to confirm the fixes are effective. Some firms charge separately for retesting, which can add significantly to the total engagement cost. Look for providers that include retesting as part of the standard engagement.
What SaaS Companies Should Look for in a Penetration Test Report
Your penetration test report needs to serve multiple audiences. Developers need technical detail and reproduction steps. Your security team needs risk ratings and remediation priorities. Executives and board members need a clear summary of exposure and business impact. And your enterprise customers need evidence that you take security seriously.
A strong report for a SaaS company should specifically address:
- Tenant isolation findings — any instance where cross-tenant access was possible, with detailed exploitation steps
- API-specific vulnerabilities — categorized by endpoint and severity, with request/response evidence
- Cloud configuration issues — IAM misconfigurations, exposed storage, network segmentation gaps
- Authentication and session management — any weaknesses in login flows, token handling, or session lifecycle
- Compliance mapping — findings mapped to relevant compliance controls (SOC 2, PCI DSS, etc.) if applicable
This report becomes a tool you can share with enterprise prospects, auditors, and your own board to demonstrate that your security program is real and effective.
Common Mistakes SaaS Companies Make with Penetration Testing
Testing Only the Web Application
Many SaaS companies scope their penetration test to just the web front-end and miss the API layer, cloud infrastructure, and multi-tenant isolation. If your test does not cover the full stack, you are getting a partial picture.
Waiting Until a Customer Asks for It
The best time to get a penetration test is before an enterprise prospect asks for your report. Proactive testing gives you time to fix issues and demonstrates mature security practices. Reactive testing under deadline pressure often results in a rushed engagement with limited scope.
Choosing on Price Alone
Penetration testing is a skilled, manual service. Providers offering significantly below-market pricing are almost certainly relying on automated scanning rather than manual testing. Our guide on penetration testing costs in Canada breaks down what you should expect to pay and what drives pricing.
Not Retesting After Remediation
A penetration test is only valuable if you fix the findings. And fixes are only trustworthy if they are validated through retesting. Skipping remediation retesting means you have no assurance that your patches actually work.
How DarkPoint Approaches SaaS Penetration Testing
DarkPoint Security specializes in penetration testing for SaaS companies and cloud-native platforms. Every engagement is led by OSCP, OSCE, and OSWE certified consultants who perform the majority of testing manually, going well beyond what automated tools can detect.
Our SaaS penetration testing engagements typically include:
- Full-stack coverage — web application, APIs, cloud infrastructure, and external network testing in a single engagement
- Multi-tenant isolation testing — dedicated testing with multiple tenant accounts to validate data separation at every layer
- Cloud-native expertise — deep experience with AWS, Azure, and GCP environments including container, serverless, and microservice architectures
- Compliance-ready reporting — reports structured to support SOC 2, PCI DSS, and ISO 27001 audit requirements
- Complimentary retesting — remediation validation is included with every engagement at no additional cost
We work with SaaS companies ranging from early-stage startups preparing for their first enterprise customer to established platforms managing complex multi-cloud environments.
For more on how to prepare your team and environment for a penetration test, see our guide on how to prepare for a penetration test.
Conclusion
SaaS companies face a unique set of security challenges that demand more than automated scanning and checkbox compliance. Multi-tenant architectures, API-first designs, cloud infrastructure, and continuous deployment cycles all expand the attack surface in ways that require skilled, manual penetration testing to evaluate properly.
The right penetration testing provider for a SaaS company understands these challenges, tests beyond the surface layer, and delivers reporting that serves your developers, your security team, and your customers.
Ready to secure your SaaS platform? Contact us to discuss a penetration testing engagement tailored to your platform’s architecture and compliance requirements.