
Why Fintech Companies Face Higher Security Risk
Fintech companies handle payment credentials, bank account details, investment portfolios, PII, and transaction records through internet-facing applications. Attackers can probe these around the clock, and they do.
Financial services ranks among the most targeted industries for cyberattacks. Fintech companies catch extra attention because they ship fast, plug into third-party financial APIs, and usually run with smaller security teams than traditional banks. Regulators, payment networks, and banking partners all expect you to prove your security controls hold up under real adversarial pressure, not just on a compliance checklist.
That’s where penetration testing comes in. A well-scoped engagement finds the vulnerabilities that automated scanners miss: business logic flaws in payment flows, authorization bypasses in account management, insecure integrations with banking APIs. The kind of things an attacker will find if your testers don’t.
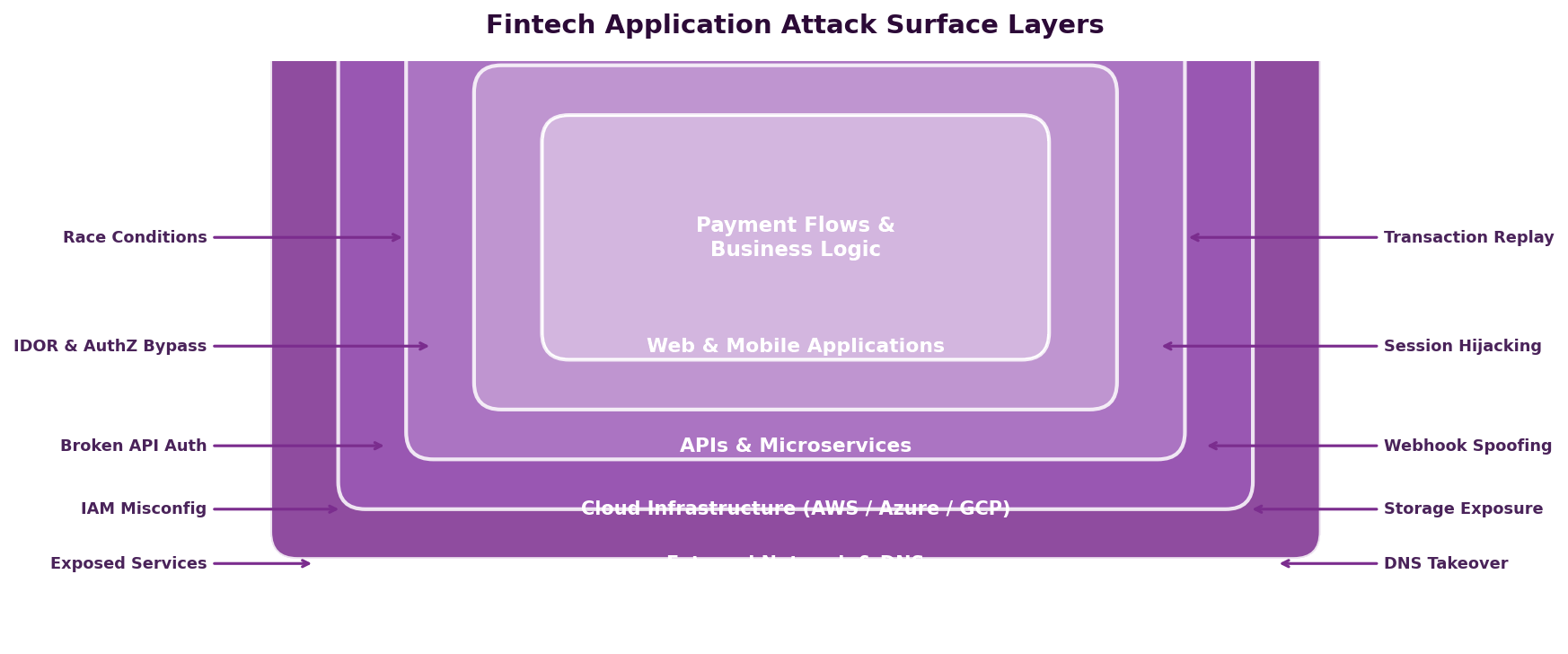
The Fintech Attack Surface
Fintech applications have a distinct attack surface that generic web application penetration testing often fails to cover. Here’s where risk concentrates.
Payment Processing and Transaction Logic
Payment flows are the highest-value targets on a fintech platform. Attackers go after them looking for:
- Race conditions in transaction processing, like submitting duplicate requests to double-credit an account or slip past balance checks
- Currency and rounding manipulation through floating-point arithmetic or conversion logic bugs that generate fractional gains at scale
- Negative amount handling, where submitting negative values reverses the direction of a transfer
- Transaction replay attacks that resubmit captured requests to duplicate payments
- Fee and limit bypasses that get around daily transfer caps, minimum balance rules, or processing fees through parameter tampering
These are business logic vulnerabilities. No scanner can detect them because they require understanding how your specific application is supposed to behave.
API Integrations with Financial Partners
Fintech platforms don’t operate in isolation. You’re connected to banking partners, payment processors, credit bureaus, KYC/AML providers, and card networks through layers of API integrations. Each one is a potential entry point:
- Insecure storage of partner API keys and tokens
- Webhook validation failures that let attackers spoof callbacks from payment processors
- Man-in-the-middle risks on partner API communications
- API responses that return more data than your application actually needs
- Fallback logic that triggers error-handling paths and bypasses security controls
Identity Verification and KYC Flows
KYC and identity verification are gatekeeping controls. Weaknesses here enable account fraud, money laundering, and synthetic identity attacks. Testing should look at document upload and verification bypass techniques, liveness detection circumvention, account linking and ownership verification logic, and step-up authentication enforcement for high-risk actions.
Mobile Application Security
Many fintech products are mobile-first. Mobile testing should cover certificate pinning, local data storage encryption, biometric authentication bypass, deeplink handling, and the security of communication between the app and backend APIs.
Regulatory and Compliance Drivers
Fintech is one of the most heavily regulated areas of technology. Penetration testing is either explicitly required or strongly expected by every major framework that applies to financial technology.
| Framework | Pen Test Requirement | When It Applies |
|---|---|---|
| PCI DSS 4.0 | Required annually and after significant changes | Any company that processes, stores, or transmits cardholder data |
| SOC 2 | Supports Trust Services Criteria CC7.1 and CC7.2 | Expected by enterprise clients and banking partners |
| OSFI B-13 | Technology and cyber risk management expectations | Federally regulated financial institutions and their key third parties |
| PIPEDA | Recommended to demonstrate reasonable safeguards | All fintech companies handling Canadian personal information |
| PCI PIN Security | Required for entities managing PIN data | Payment terminals, ATM networks, PIN processing |
| DORA (EU) | Threat-led penetration testing (TLPT) required | Fintech companies operating in or serving the EU market |
| Cyber Insurance | Increasingly required by underwriters | Most fintech companies carrying cyber liability coverage |
DarkPoint offers dedicated PCI DSS penetration testing and SOC 2 penetration testing structured to meet the specific reporting and evidence requirements of each framework.
What a Fintech Pen Test Should Cover
A penetration test for a fintech company has to go beyond standard web application testing. You need to cover the full stack and the financial logic running on top of it.
Web and Mobile Application Testing
The customer-facing application is the primary entry point for attackers, whether it’s web, mobile, or both. Testing should cover the OWASP Top 10 as a baseline, then go deeper into payment workflows, account management, fund transfer logic, and multi-step transaction processes.
API Security Testing
Fintech platforms are API-driven. Every endpoint that touches authentication, account data, transactions, or partner integrations needs to be tested for authorization flaws, injection vulnerabilities, rate limiting gaps, and data exposure. That includes both customer-facing APIs and internal microservice-to-microservice communication.
Cloud Infrastructure
Most fintech companies run on AWS, Azure, or GCP. A cloud penetration test looks at IAM policies, network segmentation, secrets management, storage permissions, and serverless function security. Cloud misconfigurations are among the most common root causes of data breaches in financial services.
External Network Testing
Your external network attack surface includes everything reachable from the internet: load balancers, DNS, email security, VPN endpoints, and any services sitting on public IPs. Fintech companies sometimes expose staging environments, internal dashboards, or legacy services without realizing it.
Internal Network Testing
If you have an office network or internal infrastructure, internal network penetration testing simulates what an attacker could do after getting initial access through a phishing compromise, a rogue employee, or a breached VPN credential. This matters especially for fintech companies with connectivity to banking partner networks.
Social Engineering and Phishing
Financial services employees are high-value phishing targets. A phishing engagement tests whether your team can spot and resist attacks designed to steal credentials, install malware, or trigger fraudulent transactions through business email compromise (BEC).
How Fintech Testing Differs from Standard Engagements
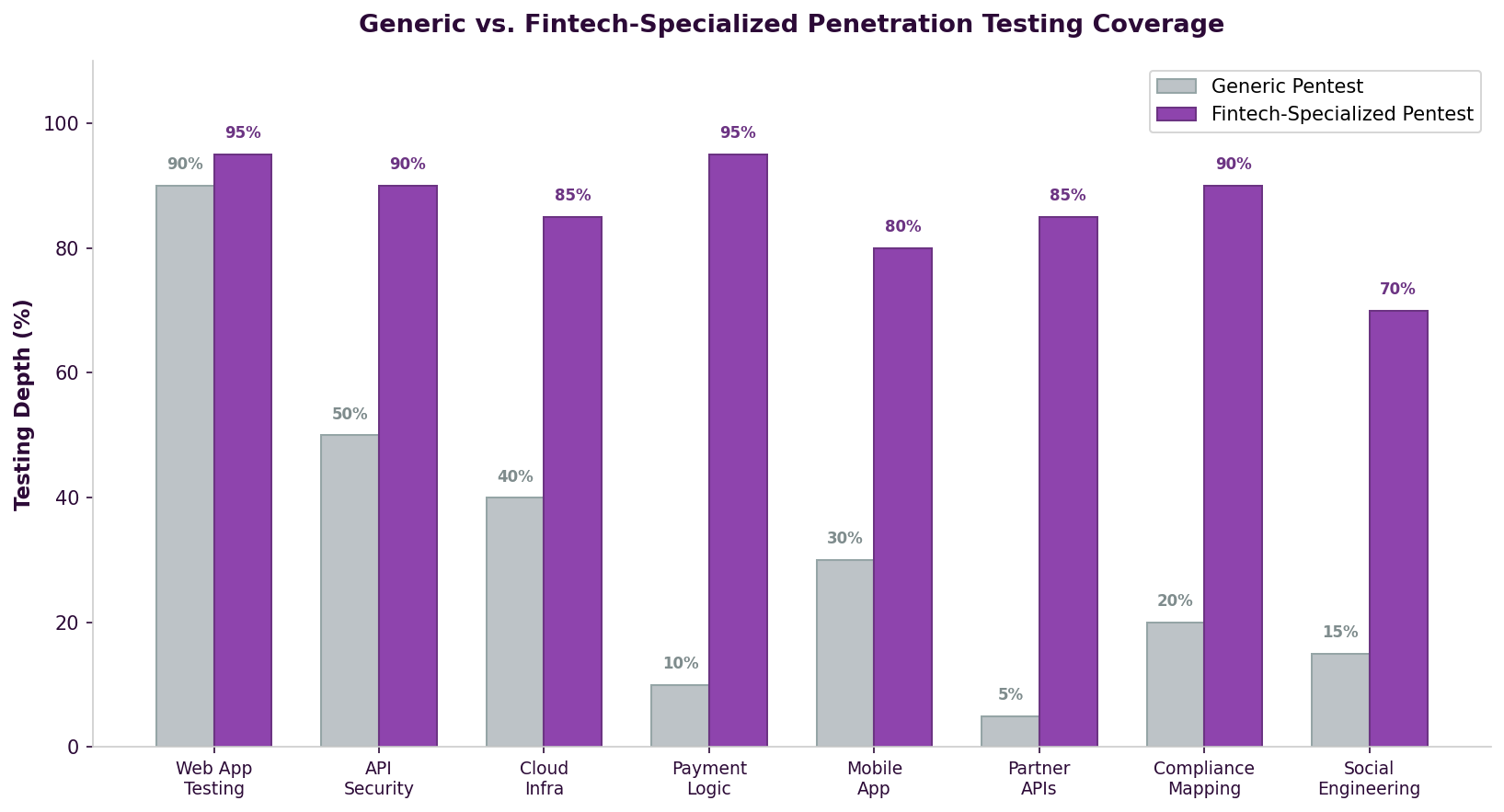
Business Logic Testing Is Required
Standard pen tests lean heavily on technical vulnerabilities: injection, XSS, authentication flaws. Fintech engagements have to spend significant time on business logic. Can someone manipulate a payment flow? Break a balance calculation? Bypass transfer limits? Exploit a multi-step financial operation? This takes testers who understand financial application behavior, not just common vulnerability patterns.
Compliance-Ready Reporting
Fintech pen test reports need to work for auditors, regulators, and banking partners in addition to your dev team. Findings should map to relevant compliance controls (PCI DSS requirements, SOC 2 criteria, OSFI expectations), and the report should include executive summary and attestation language that these stakeholders expect.
Data Sensitivity Requires Careful Scoping
Testing against production financial data takes planning. Rules of engagement must define how testers interact with real accounts, whether test accounts are used, how transaction testing avoids actual fund movement, and how any sensitive data encountered during testing is protected and destroyed afterward.
Third-Party Risk
Your banking partners, payment processors, and card networks may have their own pen testing requirements. Some require notification before testing starts. Others mandate specific methodologies or require that findings affecting shared infrastructure get reported to them directly.
Choosing a Penetration Testing Provider for Fintech
The wrong provider will run automated scans, miss your highest-risk attack surface entirely, and deliver a report that satisfies nobody.
What to Look For
- Financial services experience. Ask for case studies or references from fintech, banking, or payment processing clients.
- A manual-first methodology. Business logic vulnerabilities can’t be found with automated tools. The majority of the engagement should be manual testing.
- Relevant certifications. OSCP, OSWE, and OSCE demonstrate practical offensive skills. Be skeptical of firms that only hold theoretical certifications.
- Compliance knowledge. Your provider should understand PCI DSS, SOC 2, and financial compliance frameworks well enough to map findings to specific controls.
- Remediation retesting included in the engagement cost, not billed separately.
Red Flags
- Reports that look like scanner output with no evidence of manual testing
- Providers who can’t explain how they test business logic or payment flows
- No fintech, banking, or payment industry experience
- Won’t show you a sample report before engagement
- Fixed pricing with no scoping discussion. Effective fintech testing requires understanding your application architecture and financial workflows first.
For a broader comparison of providers, see our guide on the best penetration testing companies in Canada. For pricing context, our breakdown of penetration testing costs in Canada covers what drives engagement pricing and what to expect.
Common Mistakes Fintech Companies Make
Scoping Too Narrowly
Testing only the web application while ignoring APIs, cloud infrastructure, mobile apps, and partner integrations leaves your highest-risk surfaces untouched. Fintech pen tests should cover the full stack.
Treating It as a Checkbox
Running the bare minimum test a compliance framework requires and calling it done misses the point. Compliance-driven tests have defined scope, but your actual risk extends beyond any single framework. Use compliance as a floor, not a ceiling.
Testing Too Late
Finding critical vulnerabilities in a payment processing flow two weeks before launch creates impossible choices. Build pen testing into your development timeline so there’s time to fix findings before they reach production. Our guide on how to prepare for a penetration test covers how to set your team up for a productive engagement.
Not Testing After Major Changes
Fintech platforms evolve quickly. New payment methods, partner integrations, and infrastructure changes all shift your attack surface. Annual testing is the minimum. You should retest after any significant change to payment flows, authentication systems, or cloud architecture.
How DarkPoint Approaches Fintech Penetration Testing
DarkPoint has tested fintech platforms, payment systems, and financial applications for companies across Canada. Every engagement is led by OSCP, OSCE, and OSWE certified consultants who do the majority of testing by hand.
Our fintech engagements typically include:
- Full-stack coverage across web application, mobile app, APIs, cloud infrastructure, and external network in a single coordinated engagement
- Dedicated business logic testing of payment flows, transaction processing, balance manipulation, and financial workflow integrity
- Compliance-ready reporting with findings mapped to PCI DSS, SOC 2, OSFI, and other applicable frameworks, including executive summary and attestation language
- Testing of API integrations with banking partners, payment processors, and third-party financial services
- Remediation retesting included at no additional cost
We work with fintech companies from early-stage startups building their first payment product to established platforms processing millions of transactions monthly.
Bottom Line
Fintech companies deal with high-value financial data, complex transaction logic, extensive third-party integrations, and heavy regulatory oversight. A generic pen test won’t cut it. You need a provider that understands payment flow security, financial compliance, and the specific ways attackers go after financial technology.
Getting this wrong costs you in regulatory fines, lost banking partnerships, damaged customer trust, and breach cleanup that can threaten the business itself. A thorough pen test is one of the best investments you can make in protecting your platform and your customers.
Ready to secure your fintech platform? Contact us to discuss a penetration testing engagement built around the specific risks and compliance requirements your company faces.